Jobs and Career in Security Industry
Security encompasses measures and protocols designed to protect individuals, systems, and data from unauthorized access, harm, or damage. It involves physical security, cybersecurity, network security, and information security, each targeting specific vulnerabilities. Effective security strategies integrate risk assessment, threat detection, and response mechanisms to mitigate potential breaches. Organizations invest heavily in security technologies like firewalls, encryption, and biometric authentication to safeguard critical assets.
What are the primary sectors within the security industry?
The security industry is broad and generally divided into several core sectors, each offering unique career paths:
- Cybersecurity: Focuses on protecting networks, devices, and data from digital attacks and unauthorized access.
- Physical Security: Involves protecting personnel, hardware, and facilities from physical threats (e.g., security guards, surveillance systems).
- Information Security (InfoSec): A broader category that protects the confidentiality, integrity, and availability of data, both digital and physical.
- Personnel Security: Focuses on background checks, insider threat mitigation, and ensuring employees are trustworthy.
What is a typical career progression in cybersecurity?
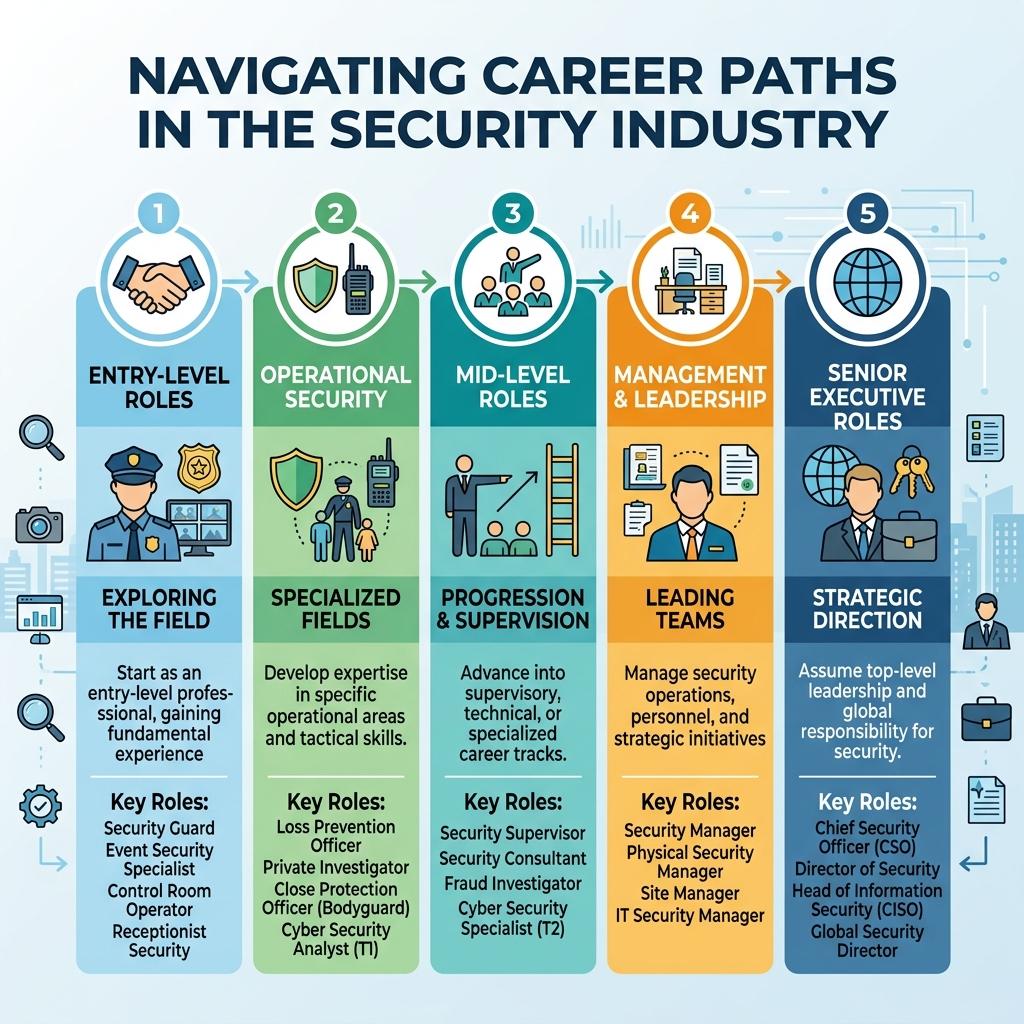
While career paths are highly flexible, a standard technical progression often looks like this:
- Entry-Level: Security Operations Center (SOC) Analyst Tier 1, Junior Penetration Tester, or IT Support with security duties.
- Mid-Level: SOC Analyst Tier 2/3, Security Engineer, or Incident Responder. At this stage, professionals specialize in offensive (red team) or defensive (blue team) roles.
- Senior-Level: Security Architect, Lead Penetration Tester, or Principal Security Consultant.
- Executive-Level: Chief Information Security Officer (CISO) or Security Director, focusing on business strategy, risk management, and compliance.
Which certifications are most valuable for a security career?
Certifications validate your knowledge and are highly regarded by employers. Here are some of the most recognized certifications:
| Certification | Target Level | Focus Area |
|---|---|---|
| CompTIA Security+ | Entry-Level | Core security concepts and baselines |
| CEH (Certified Ethical Hacker) | Mid-Level | Offensive security and hacking techniques |
| CISM (Certified Information Security Manager) | Senior-Level | Management, governance, and risk |
| CISSP (Certified Information Systems Security Professional) | Senior/Expert | Comprehensive security architecture and design |
What are the core responsibilities of a Physical Security Manager?
A Physical Security Manager ensures the safety of an organization's premises, assets, and personnel. Their daily responsibilities typically include:
- Conducting physical risk and vulnerability assessments of buildings.
- Managing security personnel, including guards and reception staff.
- Overseeing the installation and maintenance of access control systems, alarms, and CCTV cameras.
- Developing and enforcing emergency response procedures (e.g., fire drills, active shooter protocols).
- Liaising with local law enforcement and emergency services.
This role requires a blend of technological literacy for managing modern security systems and strong leadership skills.
How do salaries compare across different roles in the security industry?
Salaries vary widely based on location, experience, and specific sector (physical vs. cyber). Below is a general overview of average annual salaries in the US market:
| Job Role | Sector | Estimated Average Salary (USD) |
|---|---|---|
| Security Guard | Physical | $35,000 - $45,000 |
| SOC Analyst | Cyber | $75,000 - $95,000 |
| Security Engineer | Cyber | $100,000 - $130,000 |
| Physical Security Director | Physical | $90,000 - $140,000 |
| Chief Information Security Officer (CISO) | Cyber/InfoSec | $160,000 - $250,000+ |
What is the difference between Red Team and Blue Team roles?
In cybersecurity, teams are often divided by their operational approach to defending an organization:
| Feature | Red Team | Blue Team |
|---|---|---|
| Primary Goal | Offense (Attacking) | Defense (Protecting) |
| Key Activities | Penetration testing, ethical hacking, social engineering. | Monitoring systems, incident response, threat hunting. |
| Mindset | Think like a hacker to find vulnerabilities. | Think like a guardian to block attacks and patch systems. |
| Common Roles | Penetration Tester, Vulnerability Assessor. | SOC Analyst, Incident Responder. |
There is also the "Purple Team," which exists to ensure open communication and knowledge sharing between the Red and Blue teams.
Do I need a university degree to build a career in the security industry?
No, a university degree is not strictly necessary, particularly in cybersecurity, where practical skills often outweigh formal education. Many successful professionals are self-taught or enter the field through bootcamps and military service.
Employers typically look for a combination of:
- Hands-on experience: Gained through home labs, bug bounties, or IT roles.
- Industry Certifications: Such as Security+, OSCP, or CISSP.
- Portfolio: Documented projects or technical write-ups.
However, a degree in Computer Science or Criminal Justice can make it easier to bypass HR filters, secure management roles, or work in government and defense contracting.
How can an IT professional transition into cybersecurity?
Transitioning from general IT (like a Help Desk or Network Admin role) to cybersecurity is a very common and effective career path. Follow these steps to make the shift:
- Master the Fundamentals: Ensure you have a deep understanding of networking (TCP/IP), operating systems (Linux/Windows), and cloud infrastructure.
- Obtain Foundational Certifications: Earn credentials like CompTIA Security+ or Cisco CyberOps to validate your baseline security knowledge.
- Gain Hands-On Practice: Utilize platforms like TryHackMe or HackTheBox to practice real-world scenarios.
- Express Interest Internally: Ask to take on security-related tasks at your current job, such as reviewing logs or managing firewall rules.
What are the most in-demand soft skills for security professionals?
While technical skills are crucial, soft skills are what differentiate average security professionals from leaders. The most essential soft skills include:
- Communication: The ability to translate complex technical threats into understandable business risks for non-technical executives.
- Analytical Problem Solving: Connecting disparate pieces of data and logs to understand how a breach occurred.
- Working Under Pressure: Remaining calm and making logical decisions during high-stress situations, such as active cyberattacks or physical security breaches.
- Ethics and Integrity: Handling highly sensitive data and powerful tools responsibly, while maintaining strict confidentiality.
What are the best resources for continuous learning in the security field?
The security landscape changes daily, making continuous learning mandatory for career survival. Here are top resources to stay updated:
- Interactive Labs: Platforms like TryHackMe, HackTheBox, and RangeForce provide gamified, hands-on technical environments.
- News and Blogs: Read publications like The Hacker News, Krebs on Security, or BleepingComputer for daily threat intelligence.
- Frameworks and Communities: Study the OWASP Top 10 for application security, or the MITRE ATT&CK framework for threat tactics. Join local OWASP or DEF CON chapters.
- Podcasts: Listen to shows like Darknet Diaries or Security Now during commutes to absorb industry trends.
 jobdayta.com
jobdayta.com